How to Join AD Domain in vCenter Server Appliance 6.0 (vCSA)
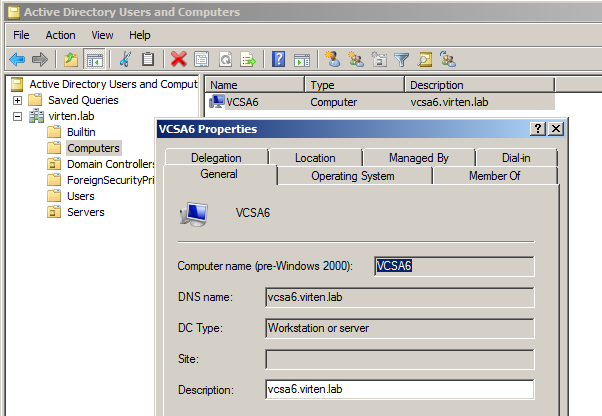
In vSphere 6.0 the vCenter Server Appliance (vCSA) has been changed a lot. Joining an Active Directory Domain is now included in the infrastructure node configuration which is part of the Platform Services Controller. Please note standard AD requirements like time synchronisation and naming. You can't join an AD if you've set an IP address as name during the VCSA guided installer.- Open vSphere Web Client (https://[vcenter]/vsphere-client)
- Login as Single Sign-On Administrator (Password set during installation)
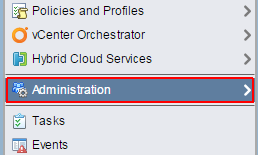
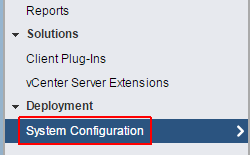
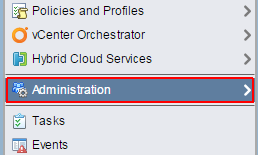
- Navigate to Administration > Deployment > System Configuration
- Open Nodes and select the infrastructure node that is associated with Single Sign-On

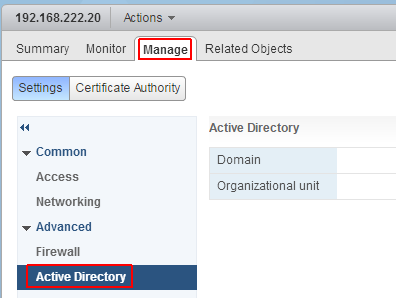
- Navigate to Manage > Advanced > Active Directory
- Click Join...
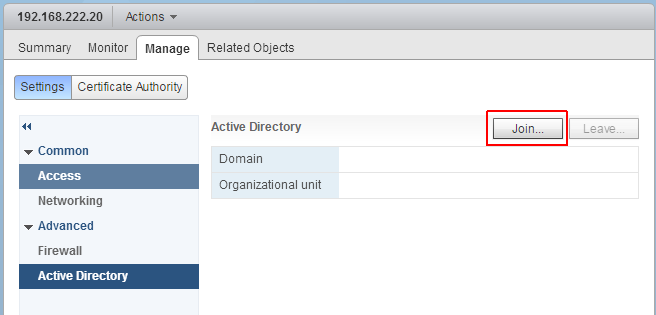
- Enter AD domain information
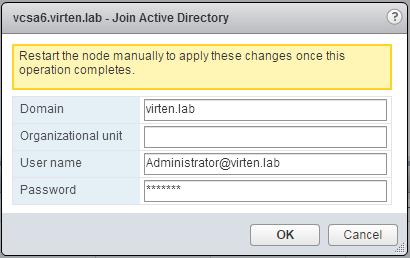
- Press OK
- Reboot the Appliance
- Open vSphere Web Client (https://[vcenter]/vsphere-client)
- Login as Single Sign-On Administrator (Password set during installation)
- Navigate to Administration > Single Sign-On > Configuration
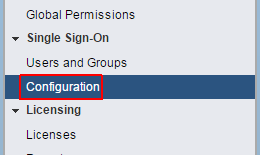
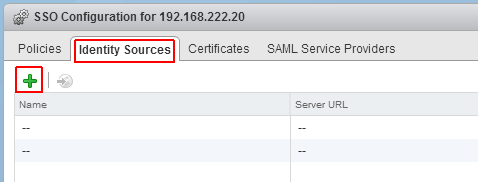
- Open the Identity Sources tab
- Click the green + to add an identity source
- Select Identity Source Type:
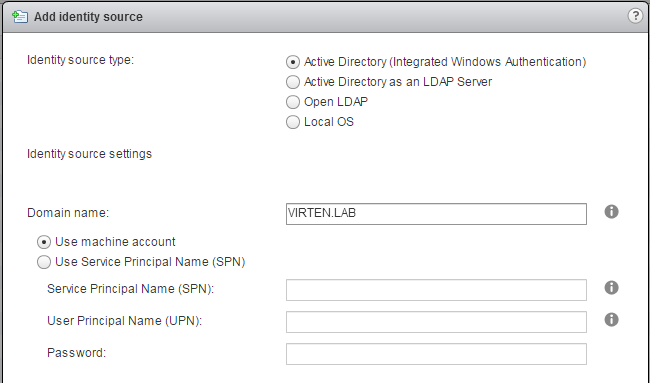
A) Active Directory (Integrated Windows Authentication)
This option works with both, Windows-based vCenter Server and vCenter Server Appliance. The underlying system (Windows Server or Infrastructure node of Platform Services Controller) has to be a member of the Active Directory domain.
 B) Active Directory as a LDAP Server
B) Active Directory as a LDAP Server
If the underlying system is not part of the Active Directory domain.Fill out the remaining fields as follows:
Name: Label for identification
Base DN for users: The Distinguished Name (DN) of the starting point for directory server searches. Example: If your domain name is virten.lab the DN for the entire directory is "DC=virten,DC=lab".
Domain name: Your domain name. Example: "virten.lab"
Domain alias: Your netbios name. Example: "virten"
Base DN for groups: The Distinguished Name (DN) of the starting point for directory server searches.
Primary server URL: AD Server URL. You can either query the local directory (Port 389), or the global catalog (Port 3268). Example: "ldap://dc01.virten.lab:3268"
Secondary Server URL
Username: A user in the AD Domain with at least browse privileges. Example virten\vcentersso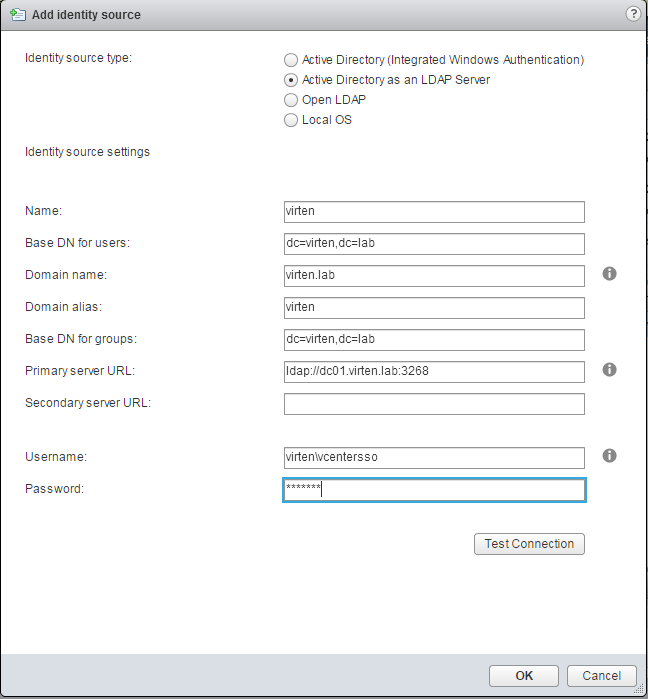
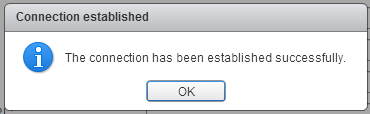
Press Test Connection to verify AD connection
- Click OK
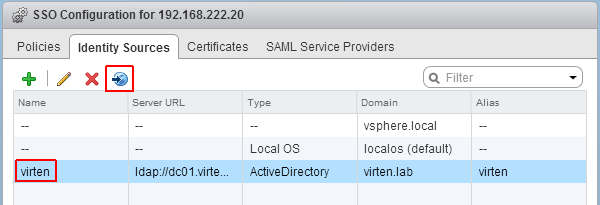
- Back at Identity Sources your AD should appear in the list and from now on you are able to assign vCenter permissions to users and groups from your active directory.
- Select you Active Directory and click the world with arrow button to make AD to your default domain.
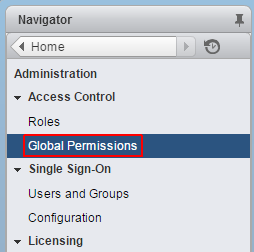
- To login with AD users, you have to set permissions. To add a AD user as global Administrator navigate to Administration > Access Control > Global Permissions
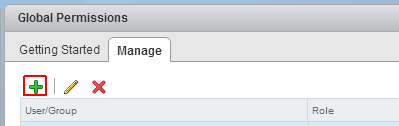
- Click Add permission
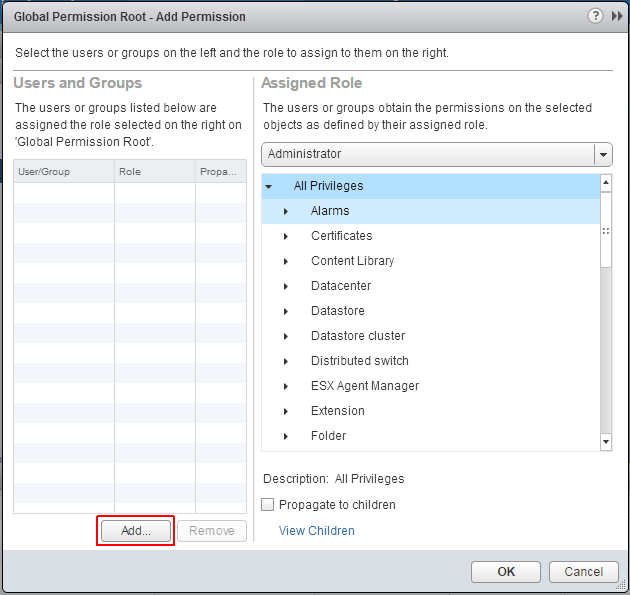
- Click Add...
- Select the Active Directory domain under Domain, choose a user and press Add
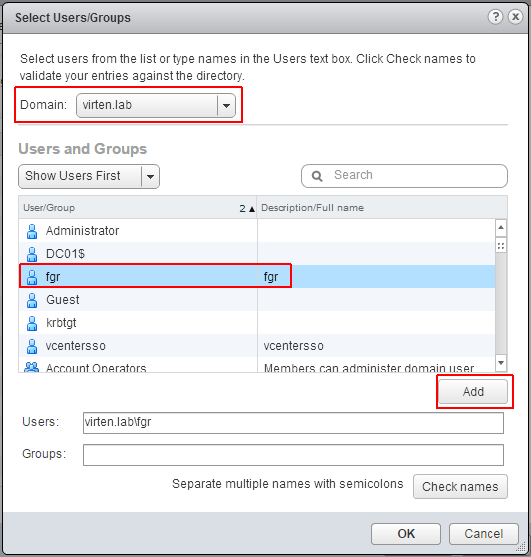
- Press OK twice
No comments:
Post a Comment